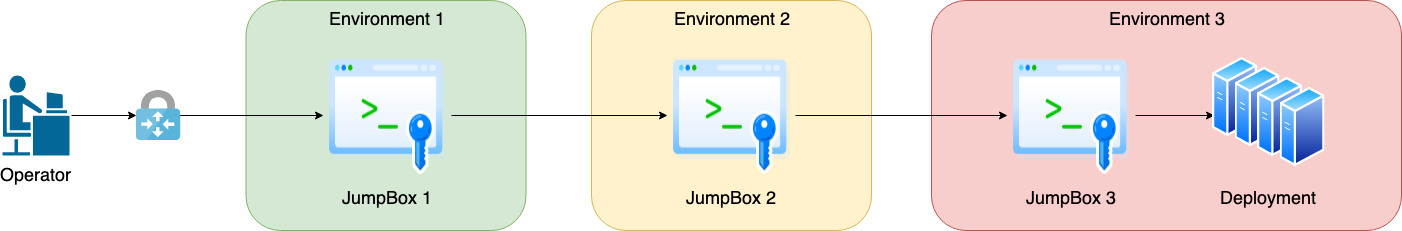
At some point, we’ve all been in an environment similar to the one shown above and had the fun experience of SSHing from one Jumpbox to the next in order to access a deployment in a more secure environment. Now if this is a rare occurrence, it isn’t a big issue. The real annoyance comes in when its a daily, hourly, or constant process and the time to jump between machines starts to really add up and impact productivity.
This is where SSH Config and ProxyJump come in to make life easier.
SSH Config
If you are not familiar with SSH Config, it is a simple configuration file for ssh that allows custom configurations to be specified and to alias those custom configurations. A simple example can be shown below that sets up TCPKeepAlive and ServerAliveInterval for all hosts, and sets up aliases for a few servers.
Host * ServerAliveInterval 60
TCPKeepAlive no
Host jumpbox-1
HostName jumpbox-1.example.com
User daviddob
IdentityFile /home/daviddob/.ssh/jumpbox-1.pem
Host jumpbox-2
HostName 10.236.156.12
User admin
IdentityFile /home/daviddob/.ssh/jumpbox-2.pem
Host jumpbox-3
HostName sec.dx.prod.c1.az1.r1a.dc1.vsp.example.com
User admin
IdentityFile /home/daviddob/.ssh/jumpbox-3.pem
Host deployment-1
HostName dep1.dx.prod.c1.az1.r1a.dc1.vsp.example.com
User daviddob
IdentityFile /home/daviddob/.ssh/deployment-1.pemThe above allows an operator to simply ssh jumpbox-1 and have the User and HostName information automatically supplied. This is useful for simplifying the process overall and reduces the need for remembering complex and long dns names or IP Addresses when trying to SSH.
So how does this help with the above scenario? With the basic config shown above an operator would still have to ssh jumpbox-1 then ssh jumpbox-2 then ssh jumpbox-3 then ssh deployment-1. Its better, but requires multiple commands, and multiple SSH configs (one on each intermediate machine) as well as SSH keys stored on each machine.
ProxyJump
This is where ProxyJump comes in. If we rework our above SSH config a bit and have all of the associated SSH keys on our local machine, we can simplify the process quite a bit. The below config simply adds the ProxyJump directive to each machine signifying which machine you need to jump through to get to the target machine.
Host *
ServerAliveInterval 60
TCPKeepAlive no
Host jumpbox-1
HostName jumpbox-1.example.com
User daviddob
IdentityFile /home/daviddob/.ssh/jumpbox-1.pem
Host jumpbox-2
HostName 10.236.156.12
User admin
IdentityFile /home/daviddob/.ssh/jumpbox-2.pem
ProxyJump jumpbox-1
Host jumpbox-3
HostName sec.dx.prod.c1.az1.r1a.dc1.vsp.example.com
User admin
IdentityFile /home/daviddob/.ssh/jumpbox-3.pem
ProxyJump jumpbox-2
Host deployment-1
HostName dep1.dx.prod.c1.az1.r1a.dc1.vsp.example.com
User daviddob
IdentityFile /home/daviddob/.ssh/deployment-1.pem
ProxyJump jumpbox-3This simple change allows an operator to ssh deployment-1, wait a bit for all of the connections to be made, and get dropped into a shell on the deployment-1 machine. So if you find yourself in a similar situation in the future, even if its only jumping through one box to get to another, maybe consider spending the 30 seconds to modify your ssh config and make the future that much easier.